Note: I practically installed Exchange Server SE role Mailbox server on Windows Server 2025. In an environment with different internal and public DNS domain and Split DNS (Split-Brain DNS). Into existing Exchange 2016 organization using DAG (Database Availability Group).
Client Access Configuration
- Exchange Server 2016 Client Access - my older article
- Configure external URLs
- Configure MAPI over HTTP in Exchange Server
We need to configure addresses (URLs) for internal and external client access. As well as the required authentication method. A client can connect to any Mailbox server and request routing (proxy) to the server where the active database for their mailbox is located is ensured.
Client Types
A client can be
- a desktop application like Outlook
- a web browser for Outlook on the web
- a mobile device
Supported Protocols and Client Access Methods
Various protocols are available for client access, with communication usually through HTTPS.
MAPI over HTTP- primary protocol for access from the Outlook application (supported since Outlook 2013 SP1), Messaging Application Programming Interface (MAPI) encapsulated in HTTPSOutlook on the web(OWA, formerly Outlook Web App) - access to the mailbox through a web browserExchange ActiveSync- protocol (based on HTTP and XML) for connecting to the mailbox from mobile devicesOutlook Anywhere- MAPI over RPC over HTTP, older option for connecting clients that don't support MAPI over HTTP (I don't understand which clients these would be, Exchange SE supports Outlook from version 2016, which supports MAPI over HTTP)POP3 and IMAP4- optional mailbox access using programs that use POP3 or IMAP4 protocol
Configuration of Internal and External Addresses (URLs) and Authentication
The services we will configure run on the Exchange Mailbox server as IIS virtual directories (Virtual Directories). Configuration can be performed using Exchange Admin Center (EAC) or Exchange Management Shell (EMS). For most situations, we can look at the settings on the existing server and configure the service on the new Exchange SE the same way.
After installing Exchange Server, its individual client services are configured with the address of that server for internal access (Internal URL). External access (External URL) is not configured. Our goal is therefore to change the internal URL and add an external URL. The service addresses used were described in the previous part, which are mail.firma.local and mail.firma.cz. Internally, the address is a DNS A record that contains IP addresses of all Exchange servers (without the new Exchange SE for now).
Outlook Anywhere
I think Outlook Anywhere is no longer used and it would be best to disable it, but this cannot be done easily.
Note: In practice, I found that Outlook sometimes tries to connect to Outlook Anywhere. The internal address must be specified in the configuration and then it depends on the host name and the certificate used (a warning pops up in case of an error, even though Outlook remains connected).
Exchange Admin Center
Configuration using EAC is located in a different place than all other services (except for POP3 and IMAP4, which we don't address here).
- EAC - Exchange Admin Center
- Servers - Servers
- select the server and click the pencil (Edit)
- switch to Outlook Anywhere
- configure Specify the external host name, Specify the internal host name, Specify the authentication method for external clients
Exchange Management Shell
Using EMS, we can list important settings for all servers.
[PS] C:\>Get-OutlookAnywhere | fl servername,external*,internal*,iis*,ssl*
ServerName : MAIL0
ExternalHostname : mail.firma.cz
ExternalClientAuthenticationMethod : Negotiate
ExternalClientsRequireSsl : True
InternalHostname : mail.firma.local
InternalClientAuthenticationMethod : Ntlm
InternalClientsRequireSsl : True
IISAuthenticationMethods : {Basic, Ntlm, Negotiate}
SSLOffloading : True
And perform necessary settings on the new server (some parameters must be specified together).
Set-OutlookAnywhere -Identity "MAIL1\Rpc (Default Web Site)" -ExternalHostname "mail.firma.cz" -ExternalClientsRequireSsl $true ` -ExternalClientAuthenticationMethod Negotiate -InternalHostname "mail.firma.local" -InternalClientsRequireSsl $true ` -InternalClientAuthenticationMethod Negotiate
Other Services - Virtual Directories
Exchange Admin Center
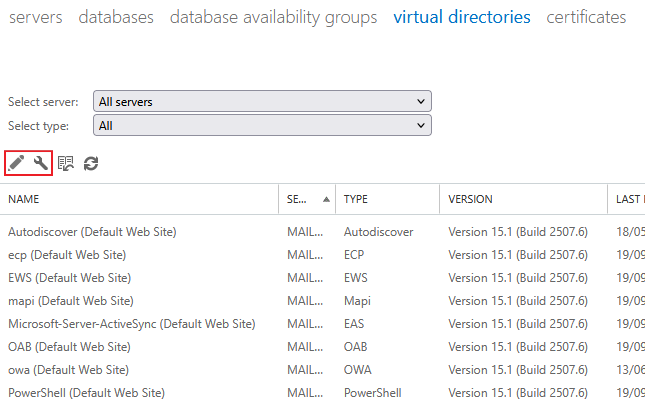
Configuration of other client access services in EAC is located in a common place.
- EAC - Exchange Admin Center
- Servers - Virtual directories
Here are virtual directories for individual services. Not just those we mentioned at the beginning.
mapi (Default Web Site)- MAPI over HTTPowa (Default Web Site)- Outlook on the web (OWA)Microsoft-Server-ActiveSync (Default Web Site)- Exchange ActiveSync (EAS)AutoDiscover (Default Web Site)- AutoDiscoverecp (Default Web Site)- Exchange Admin Center, formerly Exchange Control Panel (ECP)EWS (Default Web Site)- Exchange Web Services (EWS)OAB (Default Web Site)- Offline Address Book (OAB)PowerShell (Default Web Site)- PowerShell remote access
The address for external access can be set in bulk by clicking the key icon (Configure external access domain). Others are configured for individual servers and services.
- at the top we can filter a specific server or service type
- in the list, select the service (directory) and click the pencil icon (Edit)
- for most services we can configure internal and external URL and authentication
Exchange Management Shell
Using EMS, we can list important settings for individual services (directories) on all servers.
Main Services
Get-MapiVirtualDirectory | FL Server,external*,internal*,iis* Get-OwaVirtualDirectory | FL ServerName,externalurl,internalurl,*auth*,LogonFormat Get-ActiveSyncVirtualDirectory | FL Server,external*,internal*,*authenabled*,*certauth,*ssl*
Additional Services
Get-WebServicesVirtualDirectory | FL Server,external*,internal*,*Authentication Get-OABVirtualDirectory | FL Server, external*,internal*,*Authentication,*SSL Get-EcpVirtualDirectory | FL Server, external*,internal*,*Authentication Get-PowerShellVirtualDirectory | FL Server, external*,internal*,*Authentication,*SSL
Autodiscover We don't configure URLs on the virtual directory, but only authentication. Domain clients also use the SCP (Service Connection Point) object in AD to find the address.
Get-AutodiscoverVirtualDirectory | FL Server,*Auth* Get-ClientAccessService | FL Name,*Enabled,*Uri,*Site*
Setting Internal and External Addresses Using EMS
Internal and external addresses can be easily configured using EMS.
$s = "mail1" $urlI = "mail.firma.local" $urlE = "mail.firma.cz" Get-MapiVirtualDirectory -Server $s | Set-MapiVirtualDirectory -InternalUrl https://$urlI/mapi -ExternalUrl https://$urlE/mapi Get-OwaVirtualDirectory -Server $s | Set-OwaVirtualDirectory -InternalUrl https://$urlI/owa -ExternalUrl https://$urlE/owa Get-ActiveSyncVirtualDirectory -Server $s | Set-ActiveSyncVirtualDirectory -InternalUrl https://$urlI/Microsoft-Server-ActiveSync ` -ExternalUrl https://$urlE/Microsoft-Server-ActiveSync Get-EcpVirtualDirectory -Server $s | Set-EcpVirtualDirectory -InternalUrl https://$urlI/ecp -ExternalUrl https://$urlE/ecp Get-WebServicesVirtualDirectory -Server $s | Set-WebServicesVirtualDirectory -InternalUrl https://$urlI/EWS/Exchange.asmx ` -ExternalUrl https://$urlE/EWS/Exchange.asmx Get-OabVirtualDirectory -Server $s | Set-OabVirtualDirectory -InternalUrl https://$urlI/OAB -ExternalUrl https://$urlE/OAB Get-PowerShellVirtualDirectory -Server $s | Set-PowerShellVirtualDirectory -InternalUrl https://$urlI/powershell ` -ExternalUrl https://$urlE/powershell Get-ClientAccessService -Identity $i | Set-ClientAccessService -AutoDiscoverServiceInternalUri https://$urlI/Autodiscover/Autodiscover.xml
Authentication Methods
Choosing an appropriate form of authentication considering the type of service and specific conditions is a significant and rather complex task. I already dealt with this during the transition to Exchange 2016, and neither then nor now have I found any reasonable documentation. If we have currently well-configured settings, we simply perform the same configuration on the new server. But it may be appropriate to reevaluate everything.
We should use the most secure authentication method. This could be Kerberos, which we can only use internally within the domain. Even better would be Modern Auth, i.e., OAuth 2.0, but this requires ADFS or Hybrid Modern Authentication (HMA). For some services (like ActiveSync), we must typically stick with Basic authentication.
Windows Extended Protection
- Configure Windows Extended Protection in Exchange Server
- Exchange Server Support for Windows Extended Protection
It is important that after installation Windows Extended Protection is automatically enabled. If we do not meet the conditions, users who connect with Outlook from the Internet may have a problem. This is manifested in the fact that the login dialog pops up all the time.
In the Windows Security Event Log we find the Event ID 4625, Audit Failure, An account failed to log on.
Failure Reason: An Error occured during Logon. Status: 0xC000035B
The problem can be when we use SSL Bridging. Firewall or Load Balancer decrypts SSL connections from clients and establishes a new encrypted connection to Exchange. This can be used because external clients connect to a public domain and we use a commercial certificate. But in the internal network we have a non-public domain and certificates from an internal CA. And this is exactly the situation that is not supported with Windows Extended Protection.
SSL Bridging can only be used if we have the same certificate on the Exchange server and on the Firewall. The solution is to use public DNS names for Exchange web services in the internal network (usually one shared/virtual address) and set up a commercial certificate everywhere.
Kerberos Authentication for Load-Balanced Client Access
Because we use a virtual address, a common domain name (same namespace and URL), for all Exchange servers. We have load-balanced Mailbox servers where client access services run. When we want to use Kerberos authentication for a service (like MAPI over HTTP), we must create a special account in the domain and configure Service Principal Names (SPN) for it. All servers must use the same Alternate Service Account (ASA) credential.
This is described in detail in the official documentation or in the older article Exchange Server 2016 Client Access. We should no longer use RC4 on the account, so the msDS-SupportedEncryptionTypes attribute has a value like 24. Here we assume that the account is already created and we only configure it on the new Exchange servers.
Checking Current Settings
[PS] C:\>Get-ClientAccessService -IncludeAlternateServiceAccountCredentialStatus | FL Name, AlternateServiceAccountConfiguration Name : MAIL0 AlternateServiceAccountConfiguration : Latest: 25.03.2019 7:49:00, firma\EXCH2016ASA$ Previous: <Not set> Name : MAIL1 AlternateServiceAccountConfiguration : Latest: <Not set> Previous: <Not set>
Setting ASA Credential on Another Exchange Server
cd $ExScripts .\RollAlternateServiceAccountPassword.ps1 -ToSpecificServer mail1.firma.local -CopyFrom mail0.firma.local
MAPI over HTTP
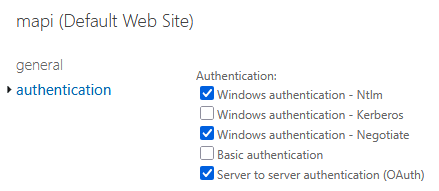
When listing settings, InternalAuthenticationMethods, ExternalAuthenticationMethods, and IISAuthenticationMethods are displayed, but in both EAC and EMS we can only set a common value (so we cannot have different internal and external methods). Using the Set-MapiVirtualDirectory cmdlet, we use the IISAuthenticationMethods parameter. The default setting is NTLM, OAuth, and Negotiate. Microsoft recommends always having oAuth configured.
Set-MapiVirtualDirectory -Identity "MAIL1\mapi (Default Web Site)" -IISAuthenticationMethods OAuth, Negotiate
Outlook on the Web (OWA) and Exchange Admin Center (EAC)
Authentication methods for OWA and EAC must be set the same. Forms Based Authentication (FBA) is often used, which uses Basic authentication in the background. We again set authentication jointly for both internal and external connections.
Configuration is easily done using EAC. For FBA, we also set the name format. But only for OWA, for ECP we always have to log in using Domain\user name. For OWA, we further configure allowed OWA features and file access. After some changes, it's necessary to restart IIS.
Exchange ActiveSync
Basic authentication is used by default, with additional options being Certificate Based Authentication (CBA) or Hybrid Modern Authentication (HMA).
Exchange Web Services (EWS)
By default, Windows authentication is used. For some cases, Basic authentication was used, which is no longer recommended.
If we have Exchange Hybrid, we should enable MRS Proxy on EWS (Enable MRS Proxy endpoint).
Outlook Anywhere (RPC over HTTP)
As we mentioned, Outlook Anywhere should no longer be needed, but we'll provide the main information anyway. Various tips can be found in the article Disable Basic authentication on the RPC (Outlook Anywhere) virtual directory.
It states that we should configure authentication using EMS because EAC only configures external settings. It's recommended to set the same methods for both internal and external access. The Set-OutlookAnywhere cmdlet has parameters InternalClientAuthenticationMethod, ExternalClientAuthenticationMethod, and IISAuthenticationMethods that set individual values. Or we can use the common DefaultAuthenticationMethod.
Get-OutlookAnywhere -Server MAIL1 | Set-OutlookAnywhere -DefaultAuthenticationMethod Negotiate
In other examples, the following configuration is often mentioned.
Get-OutlookAnywhere -Server MAIL1 | Set-OutlookAnywhere -ExternalClientAuthenticationMethod Negotiate ` -InternalClientAuthenticationMethod Negotiate -IISAuthenticationMethods Basic,NTLM,Negotiate
Configuring Download Domains
To secure attachment downloads within OWA against CSRF (cross-site request forgery) attacks, it's recommended to configure a different domain.
Checking Current Settings
Get-OwaVirtualDirectory | FL ServerName,*Download*
Configuring New Server
Get-OwaVirtualDirectory -Server MAIL1 | Set-OwaVirtualDirectory -ExternalDownloadHostName "maildownload.firma.cz" ` -InternalDownloadHostName "maildownload.firma.cz"
Outlook AutoDiscover Test and Connection Information
Directly in the Outlook application, we can perform simple checks.
- launch Outlook
- click using Ctrl + right mouse button on the Outlook icon in the notification area (next to the clock)
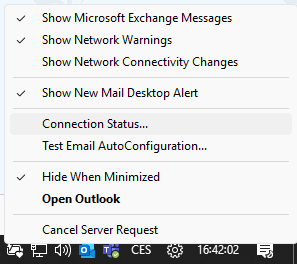
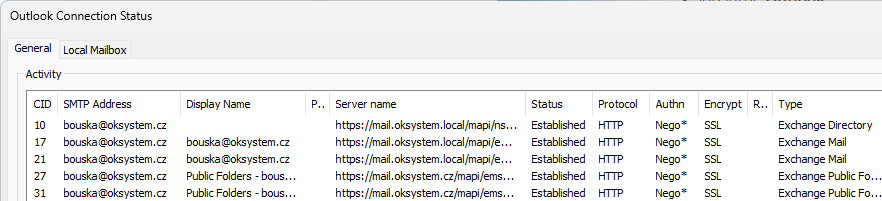
Connection Status
We can find out which Exchange servers we're connecting to, using which protocol and authentication.
- click on Connection Status
- we see individual connections to specific servers or virtual addresses, showing protocol (
HTTPfor MAPI over HTTP,RPC/HTTPfor Outlook Anywhere), URL, authentication (NEGO,NTLM,KERBEROS,CLEAR- Basic,BEARER- OAuth bearer token), encryption, and more
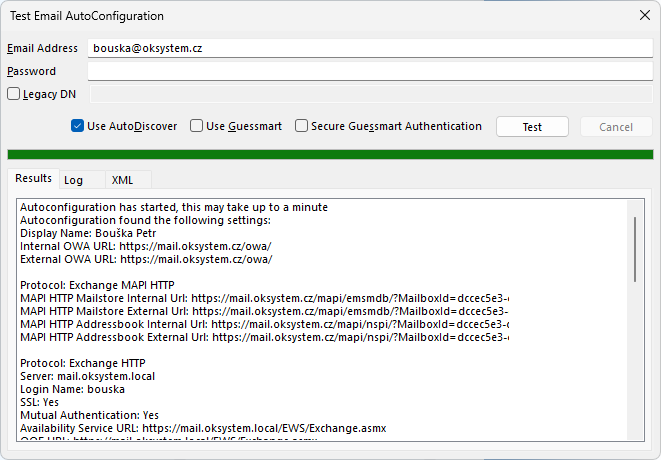
Test E-mail AutoConfiguration
We can look at the information returned by AutoDiscover.
- click on Test E-mail AutoConfiguration
- we can test the Autodiscover service, the log shows the process of finding the URL and downloading XML, with configuration data content among the results
There are no comments yet.