Note: The description in the article is based on the FortiGate FG-300E with FortiOS version 6.2.5, which is configured as an FGCP cluster and uses VDOM.
Note: The configuration as described here still worked in FortiOS 6.4. But in FortiOS 7.0 there was a major change (and allegedly a simplification) and the NAT64 and NAT46 configurations were consolidated into regular objects. I added this at the end of the article.
Address Translation Between IPv4 and IPv6 Protocols
Network Address Translation (NAT) is the term for address translation. The term NAT is usually used for translating the source or destination IPv4 address to another source or destination IPv4 address (only exceptionally is the term NAT44 used). Within the IPv4 protocol, it is widely used, mainly for translating non-public and public IP addresses. NAT66 similarly denotes the translation of IPv6 addresses. Since there are enough IPv6 addresses, there is no need to use it for this purpose.
Special cases are the translation of addresses between the IPv4 and IPv6 protocols. Simplified, we have a network with IPv6 addresses on one Firewall interface and IPv4 addresses on the other, and we want to allow mutual communication.
NAT64 denotes the translation of the source and destination IPv6 address to the source and destination IPv4 address. NAT46 conversely translates the source and destination IPv4 address to the source and destination IPv6 address. In the packet header of the IPv4/IPv6 protocol, we can only use the corresponding addresses (IPv4 or IPv6). Therefore, the source and destination addresses must be translated (Source NAT + Destination NAT). It must also be addressed how to address the destination with an address in the other protocol.
NAT64 - Translation from IPv6 to IPv4
In the article, we will describe the configuration of the NAT64 method for publishing a server with a non-public IPv4 address to an IPv6 address on the Internet.
In practice, we can solve two situations where we use NAT64:
- Publishing an IPv4 server to an IPv6 network - we use IPv4 addresses in the internal network, on the firewall we set the translation of a certain IPv6 address (on the corresponding external interface) to the internal IPv4 address of the server. In the case of IPv4 NAT, this would be Destination NAT.
- Communication of IPv6 clients to IPv4 addresses - we use IPv6 addresses in the internal network, we need to communicate to IPv4 addresses on the Internet. Similar to the use of non-public IPv4 addresses and communication to public IPv4 addresses using Source NAT. Here the problem is that the client cannot enter the destination IPv4 address. This is solved by mapping the IPv4 address to an IPv6 address. We use a defined 96-bit prefix, to which we add 32 bits of the IPv4 address. The firewall performs NAT64 and communicates to the IPv4 network. For this, the DNS Proxy (DNS64) is used, which modifies the responses to DNS queries (creates the mapped IPv6 address).
NAT46 - Translation from IPv4 to IPv6
For NAT46, we always need to define the translation of a certain IPv4 address to an IPv6 address. Theoretically, there can be two situations again:
- Publishing an IPv6 server to an IPv4 network - we use IPv6 addresses in the internal network, we use an IPv4 address to the Internet, which we translate to the IPv6 address of the server.
- Communication of IPv4 clients to IPv6 addresses - we use IPv4 addresses in the internal network, we need to enable communication to an IPv6 address. We define an internal IPv4 address (which the clients will use), which we translate to the destination IPv6 address.
Dual Stack - IPv4 and IPv6
If we need to handle IPv4 and IPv6, it is generally better to use the Dual Stack implementation. It is referred to as one of the methods of transition from IPv4 to IPv6 (other options are NATing and tunnels). Dual Stack means that the IPv4 and IPv6 protocols are running completely in the operating system. The entire network infrastructure must support both protocols and be properly configured. Devices have both IPv4 and IPv6 addresses and can use both protocols to communicate with others.
In DNS, A records are used for IPv4 addresses and AAAA records for IPv6 addresses. For an FQDN, there may be a record of one or both types. Clients must have a preference set for either IPv4 or IPv6. IPv6 should be preferred.
If we implement Dual Stack, it means that we have to configure everything twice. Especially in the case of the Firewall on the perimeter, we have to define new policies. It is not always clear which way a certain communication will go, as the destination may have both addresses. Therefore, monitoring and debugging is also more complex. For these reasons, it may be simpler to use NAT64 for some purposes.
IPv6 Configuration on FortiGate
Documentation
The official documentation is again poor. The main description is exactly the same in FortiOS 6 as in FortiOS 5.6, including the information that everything must be configured in the CLI. However, FortiOS 5.6 already allows configuring everything described in this article in the GUI. But there are additional configurations that must be done in the CLI.
- IPv6 (Handbook 6.0.0)
- NAT64 and NAT46 (Handbook 6.0.0)
- NAT64 policy and DNS64 (DNS proxy) (Cookbook 6.2.5)
- NAT64 and NAT46 (Handbook 6.0.0)
Online IPv6 Tests
- Ping IPv6 Test
- UltraTools Ping-IPv6
- Free IPv6 Ping Test Tool
- Website IPv6 accessibility validator
- Website IPv6/Ipv4 accessibility (CURL)
- IPv6 health check
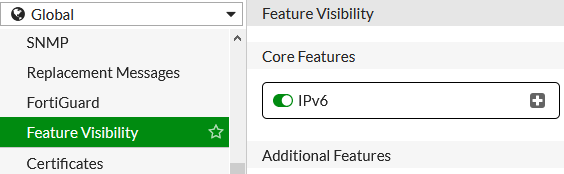
Enabling IPv6 Feature
- (Global) > System > Feature Visibility - IPv6
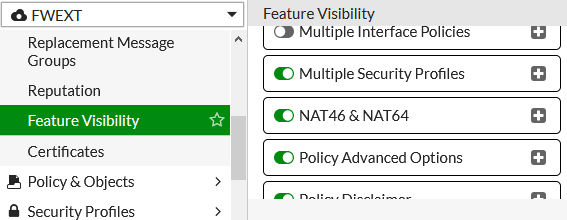
Enabling NAT46 & NAT64 Feature
- (VDOM) > System > Feature Visibility - NAT46 & NAT64
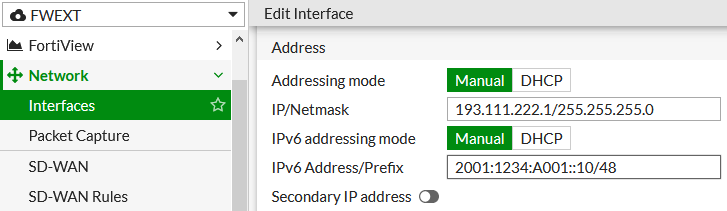
Setting IPv6 Address on Interface
- (Global/VDOM) > Network > Interfaces
- IPv6 Address/Prefix - enter the IPv6 address with a mask on the interface to the Internet
- Administrative access - IPv6 - PING - we can allow PING for testing
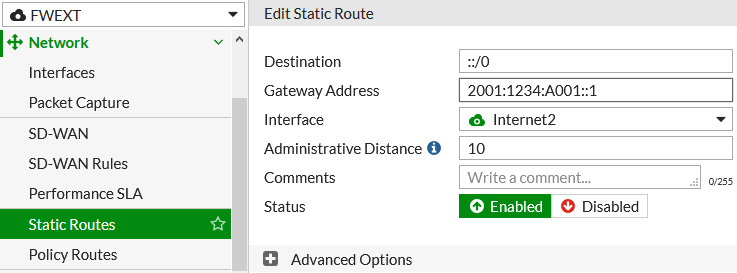
Setting Static Route
Default Gateway (Route) for IPv6 (or via SD-WAN, if used)
- (Global/VDOM) > Network > Static Routes
- Create New - IPv6 Static Route - for the destination
::/0, enter the gateway address and interface
NAT64 Configuration on FortiOS 6.2
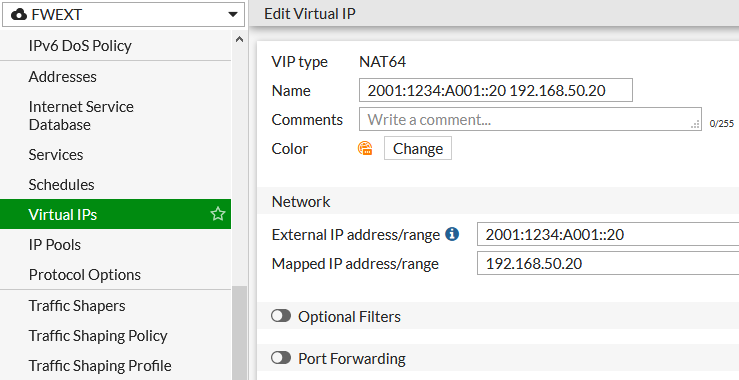
Creating a NAT64 Virtual IP
- (VDOM) > Policy & Objects > Virtual IPs
- Create New - Virtual IP
- VIP type - NAT64
- Enter the external IPv6 address and the IPv4 address to map to
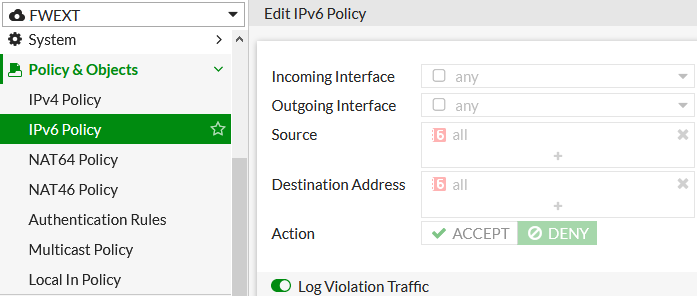
Enabling Logging of Dropped IPv6 Traffic (optional)
- (VDOM) > Policy & Objects > IPv6 Policy
- edit the Implicit Deny rule
- enable Log Violation Traffic
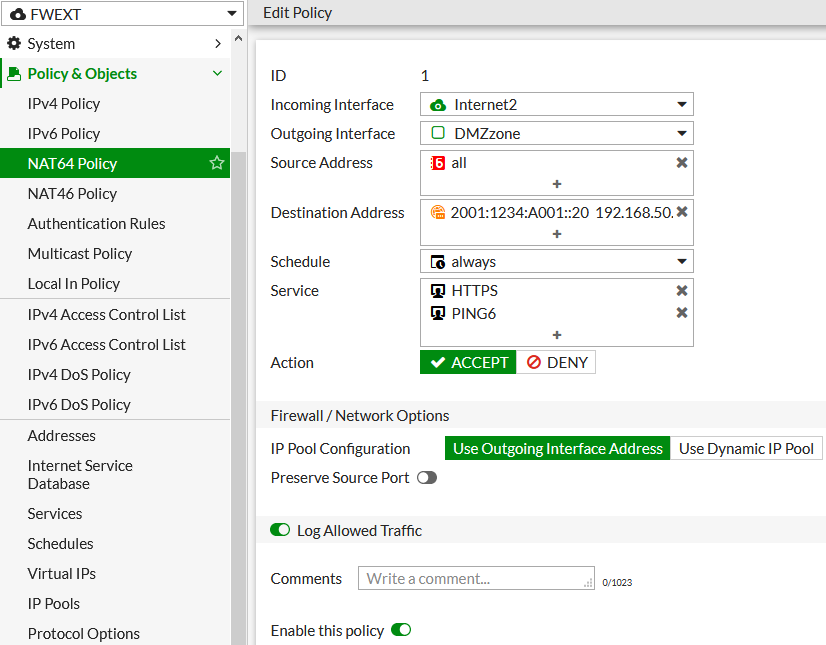
Creating a NAT64 Policy
- (VDOM) > Policy & Objects > NAT64 Policy
- standard fill in the incoming and outgoing interfaces, source addresses (
all) - set the NAT64 Virtual IP as the destination
- standard set several other options, especially the allowed services
- Source NAT is mandatory, we can choose which addresses it will be translated to
Note: I don't understand why NAT64 Policy is so limited. We can't specify a policy name. Most importantly, it's not possible to use any Security Profile.
Note: If we want to allow PING, we have to use PING6, which uses the ICMP6 protocol. It is defined in FortiOS, but hidden. We find it in Policy & Objects > Services and have to enable Show in Service List.
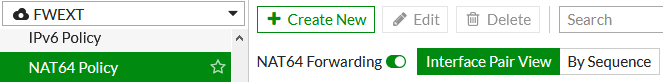
Enabling NAT64 Forwarding
Until we enable NAT64 Forwarding, the NAT64 policies will not be used.
- (VDOM) > Policy & Objects > NAT64 Policy
- top right switch NAT64 Forwarding
NAT64 Configuration on FortiOS 7.0.5
- Simplify NAT46 and NAT64 policy and routing configurations (FortiOS 7.0.0 New Features)
- NAT64 policy and DNS64 (DNS proxy) (FortiOS 7.0.5 Administration Guide)
Note: Already in FortiOS 6.4 there was a merger of IPv4 and IPv6 policies - Consolidated IPv4 and IPv6 policy configuration.
Changes Compared to FortiOS 6.2 and 6.4
In the Feature Visibility, we now only enable IPv6 and not NAT46 & NAT64. We still set the address on the interface and the static route the same as before. Below are the old commands and part of the new configuration.
config system settings
set gui-nat46-64 enable
end
NAT64 Forwarding is not enabled.
config system nat64set status enableend
The Virtual IP is no longer a special type of VIP64.
config firewall vip64
But a regular IPv6 VIP with extended settings.
config firewall vip6
edit "2001:1234:A001::20 192.168.50.20"
Here is the translation of the text in the HTML source code, maintaining the original HTML tags:
set extip 2001:1234:A001::20
set nat66 disable
set nat64 enable
set ipv4-mappedip 192.168.50.20
next
end
The special NAT64 Policy type has been removed.
config firewall policy64
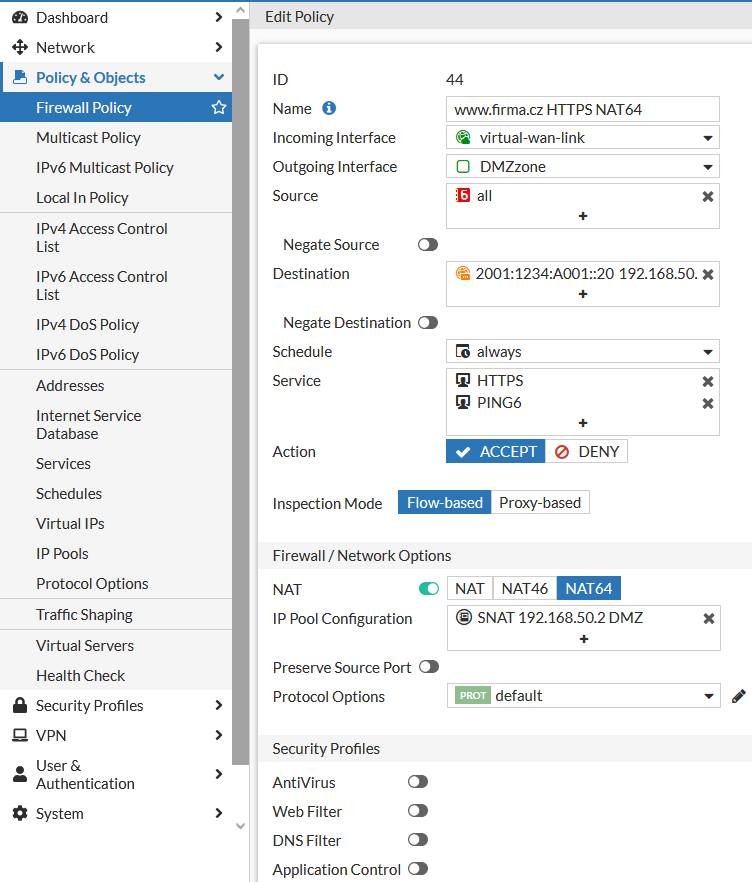
Policy is configured as a standard one (with added NAT64 settings). SNAT supports NAT64. We can apply Security Profiles.
config firewall policy
edit 44
set name "www.company.com HTTPS NAT64"
set srcintf "virtual-wan-link"
set dstintf "DMZzone"
set action accept
set nat64 enable
set srcaddr "all"
set dstaddr "all"
set srcaddr6 "all"
set dstaddr6 "2001:1234:A001::20 192.168.50.20"
set schedule "always"
set service "HTTPS" "PING6"
set logtraffic all
set ippool enable
set poolname "SNAT 192.168.50.2 DMZ"
next
end
The IP Pool has been extended to utilize NAT64.
config firewall ippool
edit "SNAT 192.168.50.2 DMZ"
set startip 192.168.50.2
set endip 192.168.50.2
set nat64 enable
next
end
The default command is set on the IP Pool and IPv6 VIP.
set add-nat64-route enable
Creating an IPv6 Virtual IP with mapping to IPv4 (DNAT)
- (VDOM) > Policy & Objects > Virtual IPs
- Create New - Virtual IP
- VIP type - IPv6
- Enter the external IPv6 address and the IPv4 address to map to
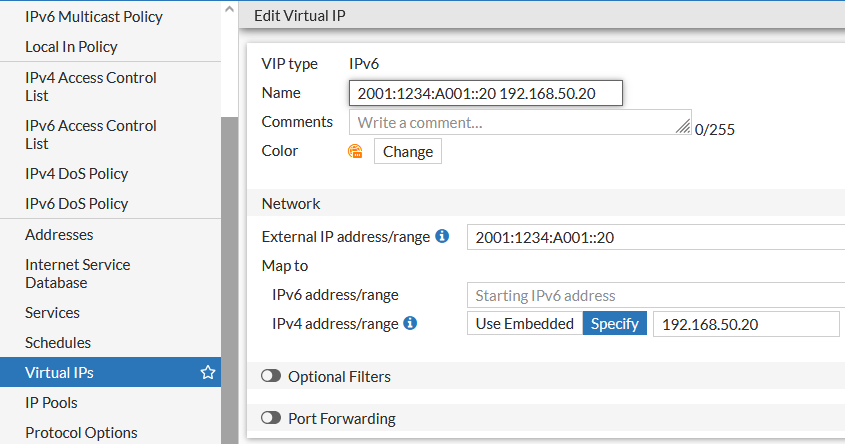
Note: In FortiOS 7.0, there is an important change. We cannot use the IP address set on the interface as the external IPv6 address. In previous versions, it worked and I use it for IPv4 NAT. I opened a ticket with support on this. Under certain conditions, the FortiGate administration interface is even accessible on this address. After some time, they replied that it is a feature of the new design (but they will fix it so that the administration interface is not displayed).
Creating an IP Pool for SNAT
- (VDOM) > Policy & Objects > IP Pools
- Create New - IPv4 Pool
- Enable NAT64 and specify the translation method
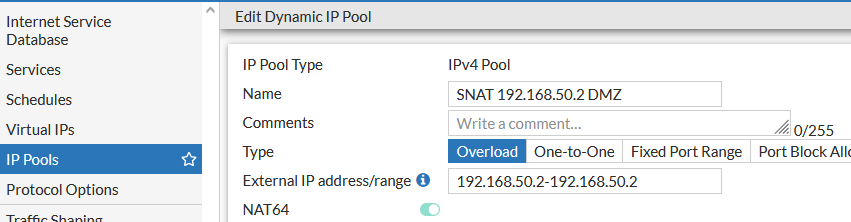
Note: Here, again, it does not work for me if I set the interface IP address to the target network as the external address. Yet for IPv4, the standard SNAT setting is to Use Outgoing Interface Address. Support did not directly respond to this, but it may be part of the first case.
Creating a policy with NAT64
- (VDOM) > Policy & Objects > Firewall Policy
- Enable Source NAT and select NAT64, choose (or create) an IP Pool (I don't know why the outgoing interface address cannot be used here, and even if I enter it in the Pool, the communication does not work)
- Fill in the incoming and outgoing interfaces, source addresses
- Set the destination to the created Virtual IP with NAT64
- Normally set other options
Note: I encountered a strange problem (bug) that I am currently solving with Fortinet support. If the IPv6 address set on the interface is used in the VIP and a policy with NAT64 (it should publish a website), the FortiGate administration interface will be displayed on this address, and the policy communication will not occur.
NAT Interface (naf.<VDOM>)
I only found a brief information. A new virtual interface (of Tunnel Interface type) was created for each VDOM, called the NAT Interface. Its name is naf.<VDOM>, for example naf.root. FortiGate uses this interface for translating requests from IPv6 to IPv4.
By default, a static route is created for the IP Pool and IPv6 VIP used for NAT64, corresponding to the specified address or range (IPv4 for IP Pool and IPv6 for VIP). We can view the routes (depending on the dashboard settings)
- (VDOM) > Dashboard > Network - Static & Dynamic Routing
If the appropriate routes are not created, the communication will not work. I encountered this in practice. The incoming communication reached the VIP (the counter increased and DNAT was visible in the log), but the policy was not applied. The communication ended with the default Deny. I tried a number of things, and in the end, what helped was that I created a VIP with a completely different IPv6 address (different range and short notation). The route was created, and since then it has been correctly created for other IPv6 addresses as well.
I'm wondering if these routes may also be related to the fact that it is not possible to use IP addresses that are assigned to an interface.
Displaying information, checks and troubleshooting
If we are solving a NAT64 problem, we can first look at the traffic log (Forward Traffic). We can capture certain traffic (Packet Capture) and look at it in Wireshark. To do a basic analysis, we can run ping and watch what happens on the FortiGate. We will use the classic Packet Sniffer, Debug Flow and Session. It may be important to check basic network things like the routing table and ARP cache.
Ping IPv6 addresses in the CLI
If we have the IPv6 protocol configured correctly on the FortiGate, we can try to ping some address on the internet (optionally we can specify ping parameters). We can use the IPv6 address directly or the FQDN, which will be resolved.
execute ping6-options repeat-count 10 execute ping6-options source auto execute ping6-options view-settings execute ping6 2a00:1450:4014:801::2004 FW1 (FWEXT) # execute ping6 www.google.com PING www.google.com(2a00:1450:4014:801::2004) 56 data bytes 64 bytes from 2a00:1450:4014:801::2004: icmp_seq=1 ttl=119 time=0.856 ms 64 bytes from 2a00:1450:4014:801::2004: icmp_seq=2 ttl=119 time=0.904 ms 64 bytes from 2a00:1450:4014:801::2004: icmp_seq=3 ttl=119 time=0.870 ms 64 bytes from 2a00:1450:4014:801::2004: icmp_seq=4 ttl=119 time=0.850 ms 64 bytes from 2a00:1450:4014:801::2004: icmp_seq=5 ttl=119 time=0.858 ms --- www.google.com ping statistics --- 5 packets transmitted, 5 packets received, 0% packet loss, time 4003ms rtt min/avg/max/mdev = 0.850/0.867/0.904/0.037 ms
Routing Table
Display the routing table for IPv4 and IPv6
get router info routing-table all get router info6 routing-table
ARP Table (Cache)
Display the IPv4 ARP table (information Technical Tip: Diagnostic ARP command information)
get system arp
Display the IPv6 Neighbor Discovery cache (the Neighbor Discovery protocol replaced the Address Resolution Protocol, using ICMP6)
diagnose ipv6 neighbor-cache list
Packet Sniffer
Capture and display packets or Ethernet frames (with a certain level of detail, in the examples value 4).
In the examples, we are capturing communication for all interfaces (any). First, only ICMPv6, then also ICMP (we would see ping on both sides of NAT64), the last one is communication of a specific IPv6 address. We stop the capture with Ctrl+C or in the last example it is 10 packets.
diagnose sniffer packet any 'icmp6' 4 diagnose sniffer packet any 'icmp or icmp6' 4 diagnose sniffer packet any 'ip6 host 2001:3de7:f006::5' 4 10
Debug Flow
Debug the traffic flow.
diagnose debug flow filter6 saddr 2001:3de7:f006::5 diagnose debug flow show function-name enable diagnose debug console timestamp enable diagnose debug flow show iprope enable diagnose debug flow trace start6 100 diagnose debug enable diagnose debug disable diagnose debug flow filter6 clear diagnose debug reset
Session
Display the list of IPv6 sessions (sessions).
diagnose sys session6 list
Díky za skvělý článek, budu rád, když budeš s Fortinetem pokračovat!
Děkuji za skvělé návody s IPv6. Není jich mnoho a jsou dost rozporuplné, tak jak se tento standard vyvíjí.
Aktuálně jsem pořídil VDSL od T-Mobile, kde bych konečně měl mít i IPv6. Bohužel to na FG nejsem schopen nastavit a podpora se zmohla jen na "to bude fungovat automaticky". Nemáte s tím prosím zkušenosti?