Note: The description in the article is based on the virtual FortiGate FG-VM00 with FortiOS version 5.6.3.
Note: I set up the FortiGate within a virtual data center, where it was offered as a virtual appliance. I didn't have much time for studying, so I solved various things through trials. The article contains my brief notes that I created along the way.
Fortinet states that FortiGate always has all the features, so we only choose the model based on the required throughput (performance). We can also purchase HW/SW support. And in addition to the firewall itself, we can purchase subscriptions for updating various definitions FortiGuard Security Subscriptions.
Comparison of different FortiGate models:
- FortiGate Virtual Appliances - specifications of virtual models
- Fortinet Product Matrix - parameters of FortiGate Network Security Platform hardware models and other appliances
- Maximum Values Table - maximum values supported by different models
- FortiOS 5.6 - features of the operating system
What some Forti-something terms (devices and services) mean:
- Fortinet - the name of the manufacturer company, https://www.fortinet.com/
- FortiGate - Next-Generation Firewall (hardware appliance), Virtualized Next-Generation Firewall (VM)
- FortiWeb - publication and protection of web servers, Web Application Firewall (WAF)
- FortiOS - operating system, The Operating System to Enable the Security Fabric
- FortiCare - hardware and software support, FortiCare Support Services
- FortiGuard - security services (subscription), FortiGuard Labs
- FortiManager - centralized management, Centralized Security Management
- FortiAnalyzer - centralized logging and reporting, Centralized Network Security Logging and Reporting
- FortiSandbox - proactive protection against threats, Top-rated Proactive Advanced Threat Detection
- FortiCloud - centralized cloud management, logging and Sandbox, Cloud-Based Management for Security and Wireless, certain features are free
- FortiClient - station security, can provide info for FortiGate, Endpoint Security, partially free
Basic documentation:
- FortiOS 5.6 Online Help
- FortiOS Help
- The Fortinet Cookbook
- FortiOS Handbook
- Fortinet Technical Discussion Forums
FortiGate VM Installation
Documentation FortiGate-VM Install Guide For FortiOS 5.6.
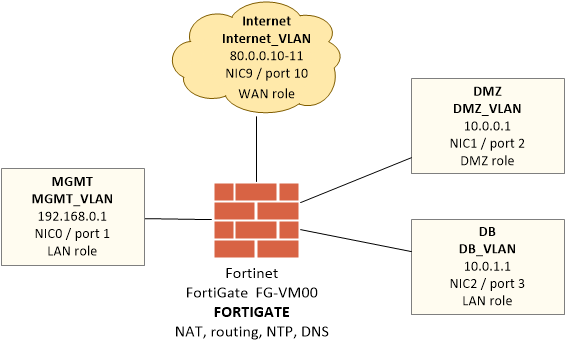
Examples given in the description are based on the following test setup. The FortiGate virtual machine has 10 network cards (NIC0 to NIC9), which are mapped inside FortiGate as ports 1 to 10. We will use 4 of them for different networks - internet (port 10), management (port 1), DMZ (port 2) and DB (port 3).
Brief initial commissioning procedure for the VM:
- create a virtual machine from the template / OVF
- set the hardware parameters of the VM, FG-VM00 version 5.6 supports 1 vCPU, 1 (or 2 GB vRAM - must be licensed already), 2GB vDisk system and 30 GB for logs (up to 2TB), 1 virtual domain (max 2)
- initially connect the port1 network - NIC0, which we set to the management network (the interface through which the device will be managed)
- connect to the console, user
adminempty password - set the IP address and administration access (at the beginning,
httpmust be enabled, because before entering the license it only supports low-strength encryption)
config system interface edit port1 set ip 192.168.0.1 255.255.255.0 append allowaccess http append allowaccess ping end
- if necessary, we set the gateway for this network
config router static edit 1 set device port1 set gateway 192.168.0.254 end
- to test the communication, we can use ping to some address in the network
execute ping 192.168.0.10
- connect to the web interface https://192.168.0.1
VDOM - Virtual Domains
Documentation VDOM configuration.
FortiGate supports creating multiple Virtual Domains (VDOMs) on a single device, and thus hosting multiple separate FortiOS instances that have independent management and allocated resources.
Basic configuration and control
Just briefly, where to find the usual things.
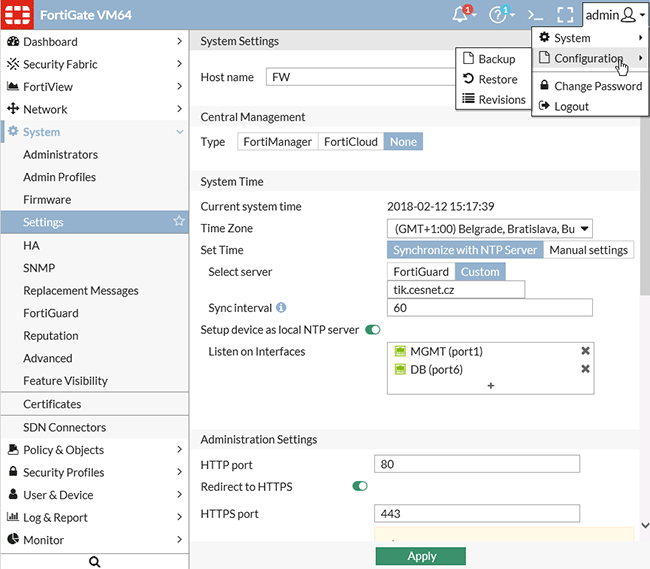
- hostname, date - System > Settings
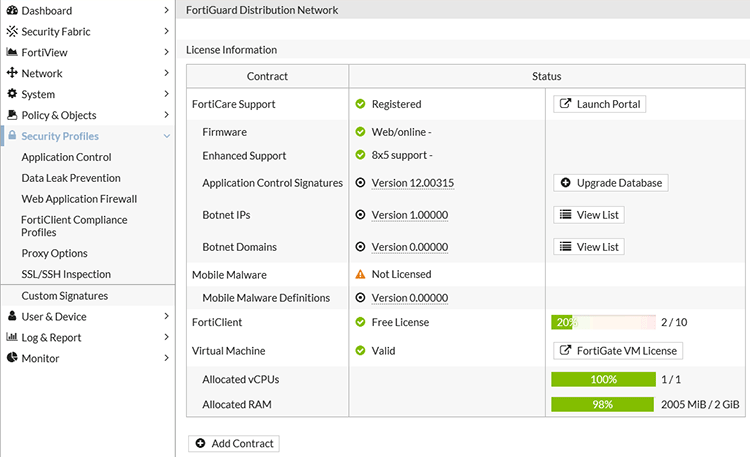
- upload license and view HW info - System > FortiGuard (after uploading the license, a restart is performed, then it took me a long time to log in, with the login saying I was entering the wrong password, when the login worked, subsequent restarts were fine)
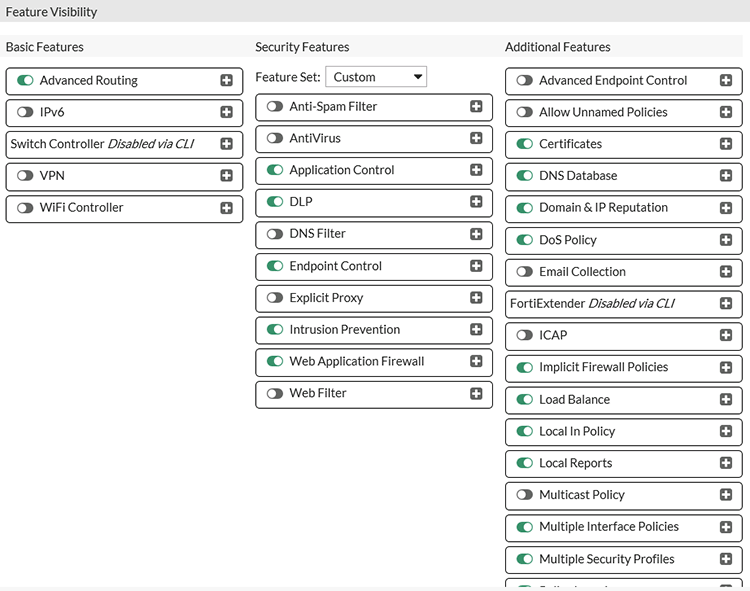
- set the properties offered by the interface (many things are hidden by default) - System > Feature Visibility - e.g. DNS Database, Local In Policy, Multiple Interface Policies, Load Balance
- change password and accounts - top right admin - Change Password, System > Administrators
- backup - top right admin - Configuration - Backup
- shutdown - top right admin - System - Shutdown
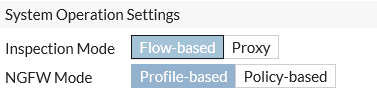
Basic operating mode
Documentation NAT/Route Mode vs. Transparent Mode, Inspection Mode, NGFW Policy Mode, Inspection Modes.
The configuration is in System > Settings.
FortiGate can operate in two main operating modes (Operation Mode):
- NAT/Route - the standard mode for most situations, FortiGate acts as a gateway or router between networks, allows the use of NAT and hiding internal addresses
- Transparent - in transparent mode, FortiGate does not make any IP address changes, it only performs security inspection of the traffic, it is placed between the internal network and the router. Switching to this mode is done via the CLI.
And in two inspection modes (Security Profile Inspection Mode):
- Proxy - the preferred mode according to Fortinet, which offers more features and configuration options (e.g. Web Application Profile, Explicit Web Proxy, WAN Optimization, Web Caching), the traffic is buffered (reconstructed) and thoroughly inspected before the action is determined, so the inspection is more accurate and the analysis is more secure, in this mode a combination of flow-based and proxy-based inspection is used, for Virtual Server we can use all types HTTP, TCP, UDP, IP, HTTPS, IMAPS,POP3S, SMTPS, SSL.
- Flow-based - the traffic is analyzed as it passes through FortiGate, so not all features are available, but it doesn't delay the traffic and offers higher performance, it uses a single-pass Direct Filter Approach (DFA) pattern matching to identify attacks, in this mode we can use Virtual Server only of type HTTP, TCP, UDP, IP.
Additional options are available from FortiOS 5.6:
- Transparent Web Proxy - we can use it for Proxy inspection mode, it doesn't have as many options as Explicit Web Proxy, but no configuration is required on the client
- NGFW mode - if we set the Flow-based inspection mode, we also choose the NGFW mode Profile-based, it works as before by creating Application Control or Web Filtering profiles, or Policy-based, where we enter applications and URL categories directly into the rule (policy), SSL/SSH inspection is applied to all rules and SNAT is also defined centrally and not on individual rules
Network and address configuration
Documentation Installing a FortiGate in NAT/Route mode, Example network topologies, Behaviour on the GUI of the Interface Role.
Interfaces
The interfaces are
- Interface - Physical or Virtual (VLAN, VPN tunnel, etc.)
- Zones - a group of multiple Interfaces (then they cannot be used individually)
- Virtual Wire Pair - port mirroring
We can assign a certain role to them, which only hides some items in the GUI when editing the interface, and is used in the logs.
- Undefined - displays everything
- WAN - internet connection
- LAN - end devices
- DMZ - servers
Configuration Network > Interfaces. The VM has 10 ports available, we will assign them to a specific network within the virtualization. We assign an alias and an address.
- port 1 - MGMT_VLAN, MGMT, 192.168.0.1/255.255.255.0
- port 2 - DMZ_VLAN, DMZ, 10.0.0.1/255.255.255.0
- port 3 - DB_VLAN, DB, 10.0.1.1/255.255.255.0
- port 10 - Internet_VLAN, Internet, 80.0.0.10/255.255.255.0

For each port, we fill in
- Alias - descriptive name of the port (interface)
- Role - WAN, LAN, DMZ, Undefined
- for the internet Estimated Bandwidth according to the connection speed, e.g. 100000 kbps
- Addressing mode - Manual, the interface IP address (usually then serves as the GW for the given network, for the internet it is the NAT address) along with the mask
- Administrative Access - allow communication on the interface, especially on MGMT (allows access to the GUI, SSH), on others perhaps ping
- on internal networks, enable Device Detection
- for the internet, choose Secondary IP Address and enter additional public IP addresses (there is a limit of 32 addresses, it may not be necessary to enter the addresses here, but just create a FW rule and the address will be used)
- if we want to disable the interface, it's the last line Interface State

Default Gateway
Configuration Network > Static Routes
We create a new route with the destination 0.0.0.0/0.0.0.0, GW 80.0.0.1, interface port10
We don't need to define other routes for directly connected interfaces. The behavior, such as routing or NAT, is handled on the individual rules and there can be one rule with NAT and another with routing.
DNS and DNS Server
Documentation Networking > DNS.
FortiGate needs to use DNS services for translating various addresses. By default, it uses its own servers, but we can set any in Network > DNS.
Another feature is that FortiGuard can serve as a DNS Server for internal clients. It then forwards queries to the configured DNS servers. But we can also create a local DNS database, i.e. a specific DNS Zone for some domain name, where we create records. In the DNS Server configuration, we choose the interface on which the service listens (on the FW IP address).
The configuration is done in Network > DNS Servers (we need to have the display of the given feature enabled). In the Interface setting, we choose the mode of operation:
- Forward to System DNS - just forwards to public DNS servers
- Recursive - first searches the internal DNS records, if not found, then forwards
Local DNS records are recommended to be operated only for internal clients (setting the Shadow zone and not Public).

NTP - time synchronization
Documentation System Settings - System Time, Technical Note: Custom NTP server configuration.
Another recommended setting is synchronizing the time with some time server. FortiGuard can again act as an NTP Server for local clients on selected interfaces. Synchronization is done either against Fortinet servers or some configured ones, but we have to perform this configuration using the CLI.
The settings are in System > Settings in the System Time section. Setting custom servers in the CLI:
config system ntp set type custom config ntpserver edit 1 set server tik.cesnet.cz next edit 2 set server tak.cesnet.cz next end
To check that the synchronization is working, we can use the command.
diagnose sys ntp status
Creating rules (policies)
Documentation FortiGate Firewall.
Configuration Policy & Objects > IPv4 Policy

We see a list of rules, which is by default sorted by interface (top right Interface Pair View). At the end is the implicit Deny.
- All rules (policies) are of one type and special situations are handled using a special object.
- To identify, we enter the name of the rule.
- The basis of each rule is the definition of one or more interfaces through which communication can enter (Incoming Interface) and exit (Outgoing Interface). This does not determine the addresses, we need to restrict them further.
- We also determine the source (Source) and destination (Destination) of the communication. We can enter an address, user or device (e.g. Android Phone). The address can be FQDN and Wildcard FQDN, Geography (country), IP Range, Subnet, Dynamic SDN Address. We can also choose
allornone. - We can determine when the rule applies (Schedule).
- Under Service we enter the allowed protocols/services (actually ports).
- As the Action, we usually choose Accept.
- Under Firewall/Network Options, NAT is set - this means Source NAT, where the source address is translated (primarily when communicating from private IP addresses to the internet).
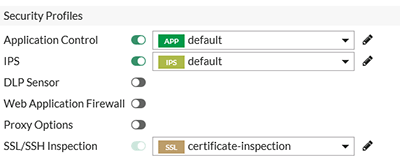
- Under Security Profiles, we set higher layer checks (IPS, Web Filter, etc.).
- We also set logging parameters in Logging Options.
- And finally, we can disable the rule with Enable this policy.
Fortinet uses the term policy, I'm used to using the term rule, so that will be used more often in the article. As stated, all rules are of one type. I personally divide the rules into two categories (although it depends on the point of view, I will use it further):
- access rule - I allow communication from one network to another for a certain protocol (destination port), often internal client access to the internet
- publish rule - I publish some service to another network, often with the help of DNAT, e.g. publishing a web server
NAT - Network Address Translation
A nice general description Source NAT and Destination NAT, NAT Configuration Examples.
For communication between two networks, we can use either routing routing or address translation NAT. When communicating to/from the internet, NAT is usually needed, because internally (LAN, DMZ) we typically use private addresses that cannot be routed within the internet.
Therefore, from the internal network to the internet, we usually use Source NAT, where the outgoing address is changed on the FW (e.g. 10.0.0.10 to 80.0.0.10). The FW stores the connection in the table, so the responses to this communication are routed to the correct internal client. If we want to communicate from the internet to a server in the DMZ that has no public address, we use Destination NAT, where the destination address is changed (e.g. 80.0.0.11 to 10.0.0.10). NAT is further divided into many variants, for example whether one address is always translated to one or more internal addresses to one public one, etc.
With NAT, port handling is also important, either all ports from the source are transferred to the destination, which we call Port Forwarding. Or in NAT we set only one port and we can send it to a different port on the destination Port Translation.
In FortiGate, the mode of communication between networks (routing, NAT) is set on each rule. In the rule, there is the Firewall/Network Options section and here the NAT checkbox. If it is disabled, routing is used for communication from the given source to the destination and the addresses are not changed. If we enable it, Source NAT is used and the source address is changed according to the further configuration. This is primarily used for outgoing communication to the internet.
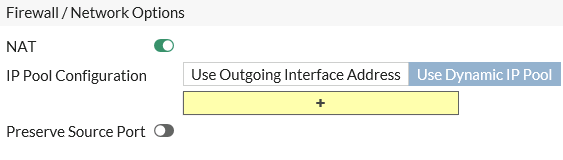
In IP Pool Configuration we can choose Use Outgoing Interface Address. Then the outgoing interface IP address is used, i.e. all sources are translated to the same address. Or we can choose Use Dynamic IP Pool and define how the translation should be done.
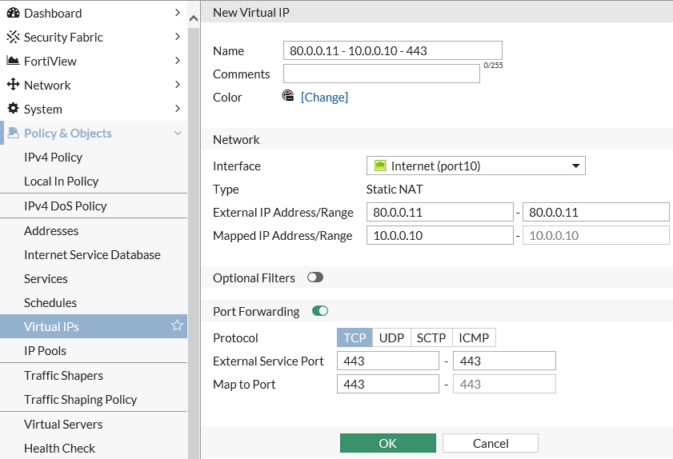
When we want to publish a server with a non-public address on some public one, i.e. Destination NAT, we need to use Virtual IPs. And we enter this Virtual IP in the rule as the Destination. For the VIP, we can specify the interface on which the address listens, then the External IP Address/Range (usually a public IP) and the Mapped IP Address/Range (usually the internal IP of the server). Optionally, we can specify additional restrictive criteria Optional Filters. In the Port Forwarding section, we can set which ports (or ranges) are forwarded and possibly forward them to different destination ports.
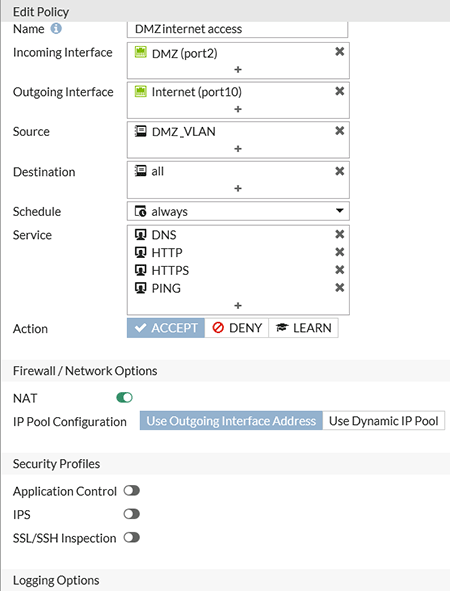
Access Policy (Policy)
Documentation Creating security policies.
General information about creating rules (policies) is described above. Here is an example of allowing certain communication (DNS, HTTP, HTTPS, PING) to the internet from an internal subnet (DMZ_VLAN).
- Policy & Objects > IPv4 Policy
- create a new rule and name it
- select Incoming Interface DMZ and Outgoing Interface Internet
- for Source, we create a new address
DMZ_VLANas Subnet 10.0.0.0/255.255.255.0 and portDMZ - Destination we choose
all - Schedule we choose
always - Service we select
pingandDNS, HTTP, HTTPS(or we can select the Service Group Web Access, which contains these three services) - Action we choose
ACCEPT - the communication is to the internet using the public IP address, so we check NAT
- we can enable certain Security Profiles, interesting is for example
Application Controlfor identifying communicating applications - Log Allowed Traffic we allow
All Sessions - we leave the rule enabled Enable this policy
- immediately after saving OK the rule will take effect
Ordering of rules
Documentation Policy order.
FortiGate uses the principle of evaluating the rules from the beginning of the list, and if the entire rule matches, it applies it and does not continue further in the list. So only one rule can be applied to each packet. Therefore, we must have more specific rules at the beginning of the list. For example, when we have some restricted traffic for a subnet, but we want to make an exception for one address, this rule must be first.
After creating a new rule, it's a good idea to look at the list and move it if necessary.
- Policy & Objects > IPv4 Policy
- choose By Sequence view
- we can drag the policy behind the sequence number to a different position
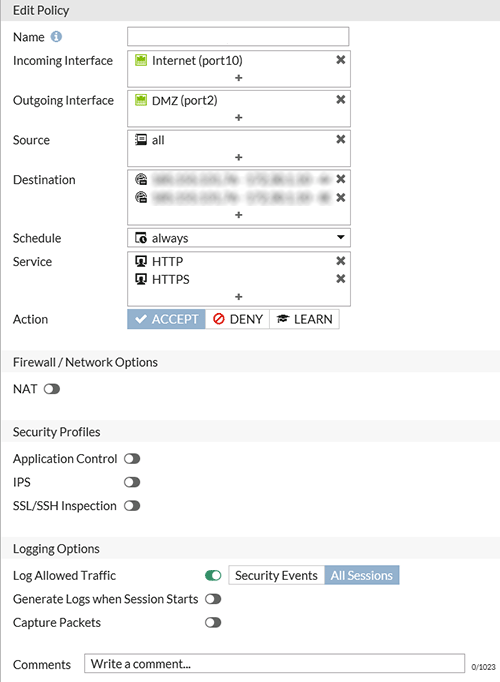
Publish Policy (Policy)
Documentation Using virtual IPs to configure port forwarding, Port forwarding, Why you should use SSL inspection, Protecting a web server with DMZ, One IP address serving multiple servers, Protecting a server running web applications.
In the example, we want to publish a web server (http and https) with the internal address 10.0.0.10 on the public address 80.0.0.11.
The publish rule is the same as the access rule and we set most of the values similarly. The basis is the creation of a Virtual IP (described in more detail in the NAT chapter). We can either create it within the rule or prepare it in advance. Here we will pre-create two VIPs (for ports 443 and 80):
- Policy & Objects > Virtual IPs
- create a new address and name it
- Interface we select Internet
- External IP Address we enter
80.0.0.11in both fields - Mapped IP Address we enter
10.0.0.10 - we enable Port Forwarding and protocol
TCP, External Service Port443we route to Map to Port443 - we do the same again for port
80
We can optionally combine these two VIPs into a single object using a Virtual IP Group. We create a publish rule (policy).
- Policy & Objects > IPv4 Policy
- create a new rule and name it
- we select Incoming Interface
Internetand Outgoing InterfaceDMZ - Source we choose
all - in Destination we select the created VIP or their group
- Schedule we choose
always - Service we select
HTTP, HTTPS(if we had routed to different ports in the VIP, we would have to enter those destination ports here) - Action we choose
ACCEPT - we don't want to change the source address, so we don't check NAT
- we can enable certain Security Profiles, interesting is for example
IPSandWeb Application Firewall, but for encrypted communication it depends on further settings - Log Allowed Traffic we allow
All Sessions - we leave the rule enabled Enable this policy
Load Balancing, Reverse Proxy and SSL Offloading
Documentation Configuring load balancing, SSL/TLS offloading.
FortiGate supports the feature of server load balancing, where the incoming traffic is distributed to one or more servers. It uses a Virtual Server to capture the incoming communication and send it to the backend server.
Note: I find the use of Virtual IPs for DNAT and Virtual Servers (where we also define Virtual IP) a bit confusing. The most interesting thing is that in the command line they are both configured the same way using the config firewall vip command.
- We define the Virtual Server IP, which is the IP address of the external interface (public IP address) to which the communication is coming.
- We specify the type (Type), which is either a general protocol IP, TCP or UDP, or a higher layer protocol (L7) HTTP, HTTPS or SSL/TLS, for which we can use advanced features (Persistence, HTTP Multiplexing). Types that use SSL are only available when FortiGate operates in Proxy inspection mode (not Flow-based).
- We also specify the port (Virtual Server Port) on which the service listens.
- And one of the load balancing methods, supported are static (failover), round robin, weighted, least session, least RTT, first alive, http host.
- We can assign up to 8 target servers (Real Servers) for load balancing.

We can also define a method for checking the server status Health Check, supported are ping, tcp, http, passive-sip.

For encrypted connections, SSL Offloading is used, where we upload the server certificate to the FortiGate, the incoming communication is decrypted and checks can be performed on it. It can also be used to accelerate the connection (encryption operations don't have to be performed by the target server). Two methods are supported:
- Client <-> FortiGate (Half Mode), where the encrypted communication is from the client to the FW and is sent unencrypted to the server
- Client <-> FortiGate <-> Server (Full Mode), where it is encrypted on both sides
We can use Virtual Server as a simpler Reverse Proxy for securing a web server. The traffic is terminated on the FortiGate and checked before being sent to the server. Unfortunately, features like Server Name Indication (SNI) and routing traffic from one IP address to different target servers based on hostname are not supported. Nor are other special options available in a sophisticated Reverse Proxy.
In order to use the SSL functions, our FortiGate model must support SSL Offloading, which we can find out in the FortiOS 5.6.3 Feature/Platform Matrix.
The configuration is easy:
- optionally we create Policy & Objects > Health Check
- we create Policy & Objects > Virtual Servers where we include the target addresses
- we create a rule Policy & Objects > IPv4 Policy, where we use the virtual server as the Destination
Many special settings (e.g. specifying allowed ciphers) can only be done using the CLI FortiOS 5.6 CLI Reference - Firewall.
Note: I was looking for a way for FortiGate to redirect traffic from http to https (not port forwarding, but Location header), but it can't do that. It looked like the set ssl-http-location-conversion enable command on the Firewall VIP should do it, but it's for the SSL Offloading Half situation (i.e. https to FortiGate, but http to the target server), so when the server responds and the HTTP header Location is http, it changes it to https.
Traffic Shaping - traffic limiting
Documentation Traffic Shaping, Limiting bandwidth with traffic shaping.
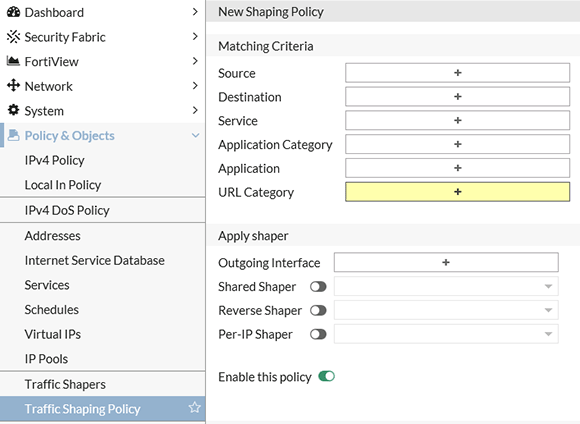
FortiGate supports ensuring Quality of Service (QoS) through prioritization and bandwidth limiting. Thanks to Traffic Shaping, we can limit the bandwidth for a particular client or a particular type of traffic, and thus ensure sufficient bandwidth and latency for the rest.
Implementing QoS is quite a complicated matter. We also have a number of settings available. The main thing is that within the Traffic Shaper we can define the Max Bandwidth, if the traffic exceeds this value, it will be dropped. And the Guaranteed Bandwidth, traffic below this level is prioritized, so the given bandwidth should be available. It also depends on the type of Shaper, we can create a Per-IP or Shared one, which by default distributes the bandwidth for all policies where it is used, or we can switch to Per Policy, where it is applied individually to each policy.
- Policy & Objects > Traffic Shapers

We then create a Traffic Shaping Policy, where we specify which traffic the limiting will apply to, and which Shaper will be applied. We specify the outgoing interface and can set a different limit for outgoing traffic (Shared Shaper) and incoming traffic (Reverse Shaper) or use a Per-IP Shaper.
- Policy & Objects > Traffic Shaping Policy
Security Profiles - FortiGuard security services
Documentation Security Profiles, FortiGuard Security Subscriptions, FortiGuard Labs.
To increase the security and visibility of the traffic for which we have created firewall rules (policies), we can apply various Security Profiles to these rules. These are a combination of various security features to protect against threats, generally referred to as FortiGuard services. Some features are free, but for the others we need to have a paid subscription.
We need to enable the security features we want to use in System > Feature Visibility. Some are only available if we have the Proxy Inspection Mode enabled.
Traffic Inspection can be done in a way that FortiGate examines the network traffic packet by packet, then performs Traffic Analysis, which is used for IPS for example. The second option is Content Analysis, where the traffic is buffered until the complete transmitted files, email messages, web pages, etc. are assembled. These are then examined as a whole, for example by Antivirus, DLP, Web Filter.
Some useful Security Profiles:
- Application Control - detects communicating applications based on various signatures, so we can then see more details in the reports, we can block various applications or their groups (not just by ports as is standard). From FortiOS 5.6.0, the FortiGuard Application Control service is free and the signatures are downloaded separately (not part of the IPS database). We can see the current version in System > FortiGuard.
- Intrusion Prevention - IPS signatures detect malicious network traffic, such as exploitation of known vulnerabilities or communication of infected clients to C&C servers, we can log or block suspicious traffic, we need an active subscription to update the definitions
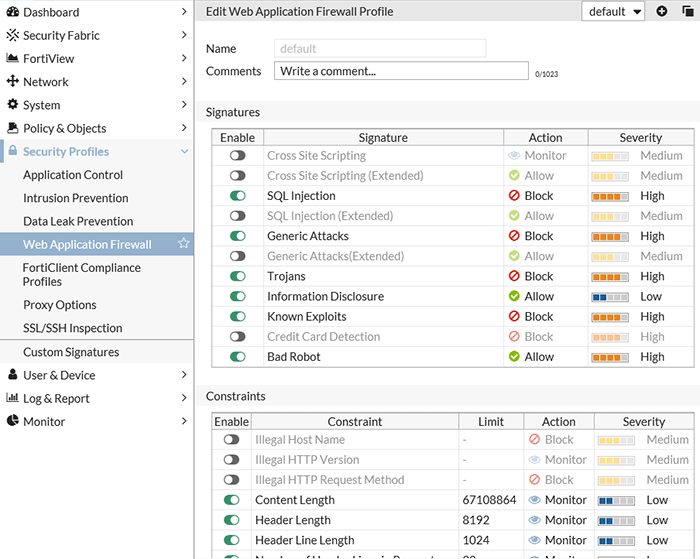
- Web Application Firewall - I didn't find any mention of this in the Security Profiles documentation, but I have this service on FortiGate, which should detect and possibly block certain attacks on published web servers, such as Cross Site Scripting and SQL Injection, or check header length, number of URL parameters, etc.
- SSL/SSH Inspection - by default, FortiGate doesn't know the content of encrypted communication, so to be able to control such communication, Full SSL Inspection (deep inspection) must be performed, where the encrypted communication is terminated on FortiGate, decrypted, and a new encrypted connection is established. FortiGate uses its own certificates - a certificate authority, which can cause a problem. When a client accesses a web site on the internet, FortiGate issues a certificate from its own authority and displays it to the client. At a minimum, this CA certificate needs to be distributed to clients as a trusted one. Additionally, there is the possibility to set exceptions for certain servers where it is not used (e.g. banks). It supports HTTPS, SMTPS, POP3S, IMAPS, FTPS and SSH protocols. Another option is to use only Certificate Inspection, where only the packet headers are checked.
- FortiClient Compliance Profile - a slightly different type of service than the others, it serves to manage FortiClient on computers
- Proxy Options - some checks defined in the Security Profile require the traffic to be held in the proxy during the inspection
For each FortiGuard service, we have some predefined profiles that specify the parameters of the given service, and we apply them to the FW rules. We can also create our own arbitrary ones.
Monitoring - logs and reports
Documentation Dashboard, FortiView , Logging and Reporting, Logging FortiGate traffic and using FortiView.
For supervision, monitoring and troubleshooting, we can use a number of features.
- Dashboard - quick view of selected information (real-time and main statistics)
- Log & Report - general work with logs (records of network traffic passing through FortiGate and actions taken) and reports (interpretation of certain information from the log), we can also set up sending alert emails
- FortiView - a monitoring system (log viewer) that integrates real-time and historical data into a single view
- Monitor - monitoring of certain properties such as routing, DHCP, Load Balance, VPN, WiFi
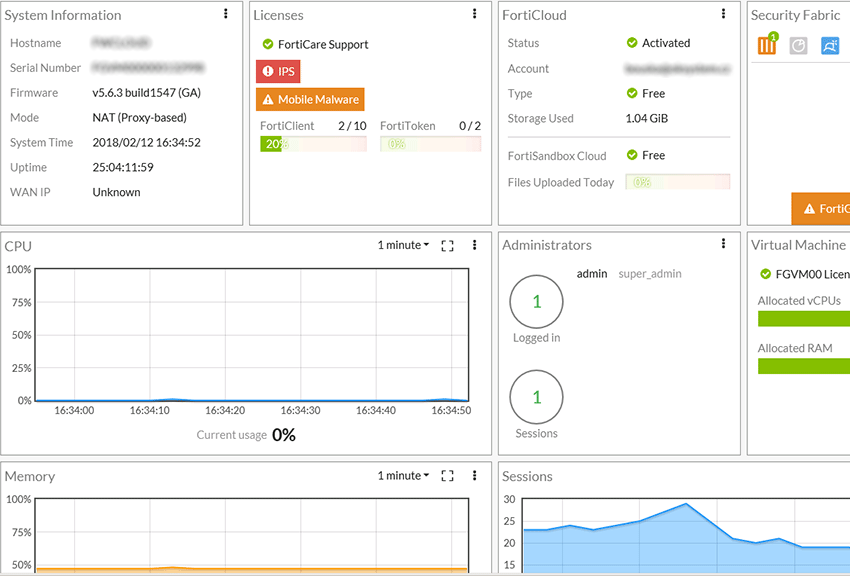
Dashboard
By default, we have the main Dashboard prepared, and we can create several more. We can place various Widgets on the Dashboard, set their position and size. The Widgets are interactive, hovering over them displays information and clicking offers actions.
There are a number of Widgets:
- One group is related to our device (system and resource utilization), we can display system information, license info, active administrators, CPU, memory, disk utilization, VM parameters.
- Then information from the Security Fabric and FortiCloud.
- And finally, we can display various traffic information, such as bandwidth on a specific port (Interface Bandwidth) and statistics/reports from FortiView (such as sources of highest traffic, used applications, etc.), where we set the display (table, graph, map) and period (instant, 5 min, 1 hour, 24 hours).
Logging and Reporting
For all functions, we must first set up logging in order to obtain any information. By default, logging is minimized to save the disk space that the logs take up. For most situations, it is suitable to enable full logging.
- Log & Report > Log Settings
- enable local logging to disk, local reports and historical data (we can also set up Remote Logging and Archiving)
- Local Traffic Log and Event Logging set to All, Display Logs From Disk
- if we want to have detailed information available, we also need to enable full logging on all rules (policies), otherwise we will be surprised that we can hardly find any traffic in the log
- Policy & Objects > IPv4 Policy - in the policy, in the Logging Options section, we set All Sessions
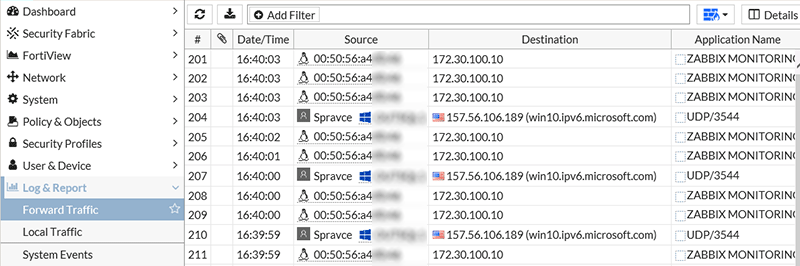
When our logging is working, we can view (and also download) the complete logs of a certain category and filter them.
- Forward Traffic - all traffic passing through the FortiGate unit
- Local Traffic - traffic to and from the FortiGate unit (Local In Policy)
- System Events and Security Audit Events - various system events
- Application Control and others - logs of certain properties, the corresponding Security Profile must be used on the policies, here for example a list of detected applications and related information
For various events, we can set up sending an informational email in Log & Report > Email Alert Settings.
The last part are the local FortiOS reports, which can be automatically generated at a certain interval and possibly sent by email. They provide a central overview of traffic and security on the FortiGate unit. Log & Report > Local Reports.
Log retention period
On two FortiGate devices I've seen, the information was that logs older than 7 days are automatically deleted. This cannot be changed in the GUI, but fortunately there is a setting in the CLI where we can set the maximum log age from 0 to 3650 days.
config log disk setting set maximum-log-age 31
We can print the current settings in the given context.
show full-configuration
FortiView
FortiView works with logs, so we must first have local disk logging enabled. In the FortiView menu, there are a number of different consoles, which are divided into categories based on the direction of traffic (using the port role assignment) on traffic from internal networks (LAN/DMZ), traffic from the internet (WAN) and all traffic (All Segments).
- There are displays of detailed information by traffic source (Sources) or traffic destination (Destinations or Servers), where we can sort by transferred data.
- Information about detected applications using Application Control (Applications and Cloud Applications).
- Under Threats are the detected threats, which can be blocked traffic or failed connection attempts.
- If we use it, we will find details on the use of Traffic Shaping, WiFi Clients, VPN, FortiSandbox.
- In the All Segments category, there are also special consoles, such as System Events, which displays certain security events on FortiOS, detected vulnerabilities Endpoint Vulnerability, geographic representation of threats Threat Map.
- Towards the end, there is a useful display of the use of FW rules/policies (Policies) and ports/interfaces (Interfaces).
- At the very end is the display of all connections (All Sessions).

Note: Some FortiView consoles, such as Applications and Web Sites, contain information only if we use the corresponding Security Profile.

The FortiView console interface has three parts by default. The top control bar, where we can set the filter and display parameters. An important thing is the time interval for which the data is displayed. The options are (depending on the FortiGate model) now, 5 minutes, 1 hour and 24 hours. We cannot display data older than one day in FortiView. There may also be a certain graph (if the display interval is at least 60s). And the data display, most often in the form of a table. The display is interactive, so we can invoke various actions. In the table rows, we can double-click to display details or filter values (Drill Down to Details).
FortiClient
Documentation FortiClient Free Downloads, FortiClient licensing, FortiGate Client limits.
We can install the free FortiClient application on clients, which consists of various components. The basic function is to detect vulnerabilities (Vulnerability Scan) on the client and enforce compliance settings (Compliance Enforcement). FortiClient registers with the FortiGate and we then obtain various information (e.g. FortiView > Endpoint Vulnerability) and the logged traffic is assigned the name of the logged-in user. Other features are VPN client, Firewall, Antivirus, Web Filter, SandBox, SSO.
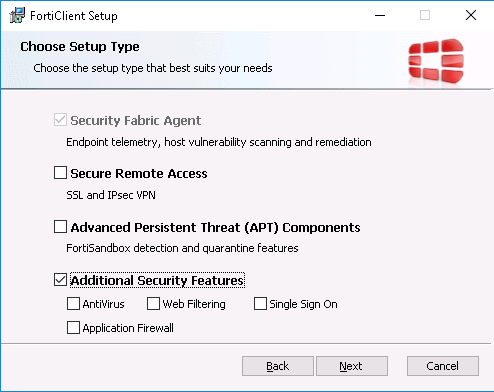
According to the information, the standalone FortiClient does not require a license (so we can use it as a home antivirus, for example). If we want to manage it from the FortiGate, we have a free license for 10 clients, additional ones must be purchased. For further centralized management, the Enterprise Management Server (EMS) is used.
FortiCloud
Documentation FortiCloud, Central Management - FortiCloud.
Fortinet offers a web (cloud) platform for centralized management of FortiGate devices (as well as FortiWiFi and FortiAP). We connect one or more FortiGate units to FortiCloud and get the ability to store logs and process them (Analyse), manage configurations (on supported platforms), back up configurations, remote access to devices (Management) and Sandbox (Advanced Threat Detection, a simulation environment where objects are placed and detected whether they are malicious).
Interestingly, a partially limited version is free (full features require a Subscription). Without a subscription, it offers 7 days of log retention, predefined reports, and FortiCloud Sandbox with a limit of 100 files per day. FortiGate VM00 can only store logs for 7 days (added - using the CLI we can set a longer interval), which is the same as FortiCloud without a subscription (if we pay, we can have up to one year). But FortiView locally works with a history of up to 1 day, in FortiCloud we can work with longer intervals.
For setting up FortiCloud:
- on the FortiCloud website, we create a simple account
- on the Dashboard we find the FortiCloud Widget, where we see the status as inactive
- we click on the widget and choose Activate FortiCloud
- here we enter the login credentials for our account (we can also create it here), we can also immediately have log sending set up (on the first connection I got an unknown error, but after a few tries everything went through)
- we get the information that FortiCloud has been activated
- if we want to cancel the connection, on the widget we choose Logout
If we want to perform management through FortiCloud of our device, we need to enable it:
- System > Settings
- in the Central Management section, switch from None to FortiCloud
When we set this, an encrypted tunnel from FortiGate to FortiCloud is established and it allows communication from the outside to FortiGate. We can then connect from the internet to our FortiGate admin interface and remotely perform actions such as backing up the configuration. If we don't allow this, in FortiCloud we will see the device status as Management Tunnel is Down.
Setting log sending to FortiCloud:
- Log & Report > Log Settings
- in the Remote Logging and Archiving section, enable Send Logs to FortiCloud
- and set the interval
- when saving, we get the information that remote logging is not recommended to be used together with local (in my opinion it's a matter of consideration)

When viewing logs on FortiGate, for example in Log & Report > Forward Traffic, we can change the data source to FortiCloud in the top right control bar (on the icon). We can also view logs and data directly on the FortiCloud website.
Děkuji za super článek. Měl bych jen jednu otázku pochopil jsem správně že bez FortiCloudu nejsem schopen prohlížet logy starší než 1 den byť se ukládá 7 dni? Je nějaká možnost ukládat a prohlížet logy třeba za celý rok bez využití FortiCloudu (prostě lokálně)? Díky.
respond to [1]KarelS: tohle je odvislé od verze fortigate. Obecně modely končící 0 (napr. 60E) v sobě nemají disk. Pak není kam ukládat a logy se dají odkládat jen do ram, které není mnoho a ani není dobré ji logy zabírat. Modely končící 1 (např. 61E) disk mají a logy se dají ukládat tam. Pak už je to jen o konfiguraci a jejich počtu. Různé modely mají disky různé velké.
respond to [1]KarelS: V tom virtuálním modelu, který používám. Pomocí FortiView mohu prohlížet maximálně 24 hodin staré "reporty". Ale pomocí Log & Report zobrazím veškeré logy, které mám k dispozici. Ta virtuální verze mne nenechá logovat víc než týden (nevím, zda by nepomohlo zvětšit disk pro logy, ale v tuto chvíli je skoro prázdný a stejně to dovolí jen týden). Moc nechápu tato omezení.
Dobrý den obecná otázka: Jaký HW Firewall byste doporučili pro firmu cca 25 zaměstnanců. Váhal jsem mezi Kerio NG 300, Zyxell Zywall USG110 a Fortinetem (verzi si nepamatuji). Nakonec vzhledem k bídné podpoře ze strany GFI dáme přednost Zyxelu.
Nahrazujeme LinuxFW. (pár vzdálených přístupů, jinak nic speciálního nechceme). Prioritou je bezpečnost (proto měníme - chci nově antivir+multiwan) a pak cena. Díky za eventuelní tipy ...
Zywall má dobrý poměr cena/výkon sám jej momentálně provozuji (starší USG300). Nicméně se rozhlížím po něčem lepsim hlavně právě z pohledu možností monitorovat provoz a kvalitní reporting. To mi bohužel u Zywallu chybí. Co jsem se tak dívám tak se mi líbí Sophos nebo právě Fortinet i když ten jsem bohužel neměl možnost vidět v produkci.
respond to [1]KarelS:
u fortigate muzes nastavit SysLog server, na ktery je veskery logovani prehazovano a z tama muzes analyzovat
respond to [4]kyssling: rekl bych ze verze Fortigate 50E je idealni. na dalcish 10 let pokoj :)
Zajímalo by mě zda preferujete firewall jako HW applianci nebo virtuální applianci? Zatím měl vždy HW ale premyslim... zda ten Fortigate nepořídit virtuální?
Zrovna jsem se díval na ty malé appliance a optimální mi připadá FortiGate-61E, docela mne překvapila nízká cena (víc se platí za předplatné, pokud je člověk chce).
V řadě případů se více kloním k HW řešení (a zajímavé je i využití VDOM), ale někde se virtuální vyloženě hodí. A pokud si dobře zabezpečím tu virtuální vrstvu (třeba přivedení nezabezpečené linky - internet), tak proč ne.
ahoj, díky moc za nový a konečně pro mne zajímavý článek :) zajímalo by mne na základě čeho jsi vybral fortinet? tedy pokud výběr byl na tobě?
respond to [4]kyssling: mohl bych vědět víc o těch problémech s podporou ze strany GFI?
respond to [10]Michal Zobec: V cloudu to bylo jediné, co bylo k dispozici :-). Ale ještě vybírám FW na jiné místo a Fortinet je žhavý kandidát kvůli vlastnostem, rozšíření, rozhraní (to je pro mne dost důležité) a ceně.
respond to [12]Samuraj: možná by bylo fajn zrovna tyto informace uvést :) já právě kvůli tomu váhám mezi fortinetem, zyxel usg a případně kerio firewall. já teda bych upřednostnil spíše hw appliance.
respond to respond to [3]Samuraj: Samuraj: Omezeni je nejspis kvuli tomu, aby lidi ukladali napr. prave na Forticloud nebo Fortianalyzer potazmo fortimanager. Je o nejspis marketingova vec. Dalsi vec by mohla byt zivotnost disku. V pripade VM by to fortinetu mohlo byt jedno, nicmene se asi developerum toto nechtelo rozlisovat. Preci jenom prodavat HW a SW je rozdil...respond to respond to [3]Samuraj: Samuraj:
Jeste lze ukladat z fortigatu na syslog...
respond to [8]Strnadk: Virtualni firewall ma mnoho nevyhod a to je predevsim performance. V pripade FortiGateVM prijdete o hardware acceleration - content processors a network processors a security processory proste ve VMku nenajdete :). V pripade VM to vsechno tahne CPU, ktere nikdy nedosahne stejne efektivy jako vyse zmineny hardware.
Ahojte,
spravuji 5 fortin (3x 90D, 2x100D a 1x200D) a to více než 5 let, vše běží na 5.6.3 a na HW. Do VM bych nešel z mnoha důvodů viz. příspěvek od Alivo. Zatím převládá spokojenost, ale přechody mezi verzemi 5.0 -> 5.2 -> 5.4 -> 5.6 bývá někdy o nervy. Doporučuji mít HA nebo počkat na 2 až 3 release ve verzi. Téma logování je spíš marketingová záležitost, tak aby se prodávali FortiAnalyzery nebo místo na ForiCloudu. Zkoušel jsem i posílát na syslog, ale pro mě je to nepřehledné. S Forticlientem je také někdy pěkná "sranda" :-).
Pokud řešíte firewall typu NG zkuste taky ještě kouknout po Sophos UTM nebo NG. Určitě jsou si tyto firewally navzájem konkurencí, a u toho Sophosu si mužete provozovat home verzi co je free pro 50 ipček v lan.
Žádně boxy navíc nemusíte kupovat, vše je in v teto verzi jde i HA.
Dobrý den, koukám, že se tu objevil i Fortinet. Tak k tomu mám taký myslím co říct.
Rozhodovaní mezi Kerio, Zyxel a Fortinetem je myslím z hlediska bezpečnosti jednoznačné pro Fortinet. Fortigatu ostatní 2 nesahají ani po kotníky.
Nicméně jde taky o cenu a tam je zase u Fortinetu někde úplně jinde než Zyxel a Kerio.
A ještě jedna věc, i když ta bude asi u všech hodně podobná. Je to support a ochota řešit chyby, případně ochota vytvořit i pro prťavého klienta z ČR patch pro jeho prťavý firewall např. 200D, 300D. Přeci jen to jsou mezinárodní firmy a nějaký malý zákazník z "východu" je moc netrápí.
Příklad z poslední doby. Fortigate 300 v HA 5.6.2, box padá do conserve mode. Odpověď od Fortinetu: našli jsme podobné chování ve verzi 5.6.3 a je to pravděpodobně chyba wad, nebo ips enginu, oprava je ve verzy 5.6.4. Na otázku kdy že bude software 5.6.4, je odpověď hádejte, můžete dvakrát. Ano C je správně: "to nidko" neví. :-))) Takže máte firewall za 100-tisíce, ale kvůli chybě nemůžete používat ty security funkce jako IPS, web filtering, APPCTRL atd, protože tam je chyba a vytěžuje to box, tak že se sekne a vytíží se mu pamět a spadne do conserve modu, supeeer. A oprava není a výrobce neví kdy bude. A jen pro vás žádnou opravu rozhodně nenapíšou, na to jste moc malý.
Ale jak říkám, pžná takovéto scénáře existují i u jiných výrobců a Fortinet není jediný.
Pěkný článek. Před odchodem od bývalého zaměstnavatele, kde byl corporate standard firewall od CheckPointu se počítal business case právě proti Fortigate a za cenu maintenanci na CP jsme dostali nové boxy Fortigate. U implementace už jsem nebyl, ale vím, že se s tím kluci dost trápili. Údajně byl problém přímo s boxem. Teď už si to sedlo, ale podobný pohled co zmiňuje Čtvrtek je dost stejný. U stávajícího zaměstnavatele používáme Kerio Control. Přecházeli jsme z HW boxu (nějaké PCko) na VM platformu na Hyper-V v HA režimu (HP VSA, MS Cluster) a funguje spolehlivě. Přes Kerio Control přistupuje cca 30 uživatelů (klasický provoz e-mail, www, pak vzdálený přístup přes Kerio Control VPN klienta a také Citrix). S ohledem na cenu = funkcionalita POHODA. Ohledně podpory tzn. GFI je snad možné v rámci podpory řešit ZDARMA pouze jeden ticket...ostatní je placená služba. Nevím nemám zkušenost, jelikož řešení je funkční a když jsme něco řešili, tak Google vždy pomohl.
respond to [16]Alivo: Souhlasím, zůstanu u HW firewallu. Nicméně co říkáte na virtuální Fortianalyzer? Je to levnější než HW analyzer a na výkon by to již nemuselo být tak kritické... Nemáte s tím někdo zkušenost? Díky.
respond to [20]Matesovic: Trochu mimo téma, ale nedá mi to, rád bych se zeptal jak jste spokojeni s řešením HP VSA namísto HW diskového pole? Díky.
respond to [11]Michal Zobec: Dobrý den vycházím z následujících zdrojů :
http://forums.kerio.com/?t=msg&goto=136596&
http://forums.kerio.cz/m/16858/
https://www.lupa.cz/clanky/odchody-lidi-a-smirovaci-software-ceske-kerio-je-po-akvizici-od-gfi-v-rozkladu/
+ zkušenost našeho externisty ohledně dotazů na HWFW (v Zebře tomu pořádně rozumí jeden člověk ...)
Tak jsem se dozvěděl, že délka logování se nastavuje pomocí CLI :D a můžu dát mnohem více než 7 dní. Doplním do článku.
respond to [9]Samuraj: K tomu Fortigate: Na doma a do malicke firmy je velmi zajimave je FWF61E v kombinaci s FortiAP to luxusne pokrylo potreby celeho domu i laborky.
Pro firmu bych uvazoval o HA. Pak je lepsi volba model bez integrovaneho radia (FGT61E) a radia zvlast.
Pro vetsi pozadavky jsou vetsi boxy.
Vyhoda HW boxu je HW offload toho co se offloadovat da (typicky non UTM traffic).
Vyhoda VM je lepsi skalovatelnost a brutalni vykon v UTM aplikacich (mas poradne CPU) za cenu vetsiho zdrzeni.
respond to [19]Čtvrtek: Taky máte nově několik Fortigate a zatím pohoda. Jeden ticket už jsem s Fortinetem řešil (objevil jsem jim bug) a trvalo to sice hodně dlouho, ale vyřešili to. Rozhodně množství funkcí těch prvků je velké a cenově nevychází špatné.
Používáte někdo dual WAN (obě linky aktivní) na tom Fortinetu (u Zyxelu 110 jsme museli nahrát neoficiální firmware, jinak se rozpadal https protokol - online bankovnictví, datové zprávy např. nefungovaly správně)?
A jestli je tady nějaký specialista ... Mám problém s připojenými VPN klienty zvenku, čas od času se jim klient odpojuje (internet jim jede) a pomocí různých měření jsem zjistil, že máme na hlavním připojení firmy mikrovýpadky uploadu trvající třeba 5 vteřin ... Netušil jsem, že je VPN tak náročné na kvalitu připojení ...
[29]mikrovýpadek 5 vteřin? Tomu bych neříkal mikro. To bych radši vyměnil ISP. Zkoušel jsi polovit "keep alive" jak na Fortigate, tak na klientovi? Btw, používáš SSL nebo IPSec VPN ? Se "split tunnelingem" ? Jakou máš verzi FortiOS a jakou mají klienti?
[30]Děkuji za odpověď, špatně jsem se vyjádřil, používáme router Zyxel USG110. Používáme SSL. Možnost "Keep alive" jsem nalezl pouze na L2TP VPN (ne u SSL a IPSec) a "split tunneling" vůbec.
Budu muset trvat na zlepšení linky od ISP ... (download OK, ale upload mívá výpadky).